Significantly, network equipment vendors define their own product development and lifecycle management processes, applying security best practices throughout. From planning and design to implementation, building and testing — all the way to release and delivery.
What does the NESAS Process Audit involve?
In essence, the vendors assess their processes’ level of compliance to the NESAS product development and lifecycle management security requirements – as defined by the industry through the GSMA.
Then they demonstrate the implementation of and adherence to these processes to their choice of Appointed GSMA NESAS Auditor. After which, they assesses compliance to the NESAS requirements.
Frequently Asked Questions
Mobile network equipment vendors have internal processes for product development and maintenance. To develop secure products, NESAS requires that these processes integrate certain security controls. Since these reduce the risk of design flaws and implementation errors, as well as demonstrate that security maintenance of developed products is in place (e.g. patch management). Therefore, NESAS seeks to verify that the vendor has these security controls and processes in place and is adhering to them. It does this through a self-assessment and independent audit.
The audit starts with an assessment of the processes, which involves a desktop documentation review. Later, the audit team conducts and on-site audit to determine if the vendor is applying the processes in practice.
It is solely at the discretion of the equipment vendor. They choose to approach one of the GSMA-appointed auditors to request an audit of their processes. The vendor might do this because their mobile network operator customers require that the vendors they work with undergo a NESAS process assessment.
If the vendor’s processes change after the assessment, then this should trigger a re-assessment. Additionally, if further requirements are added to NESAS, this may necessitate a reassessment.
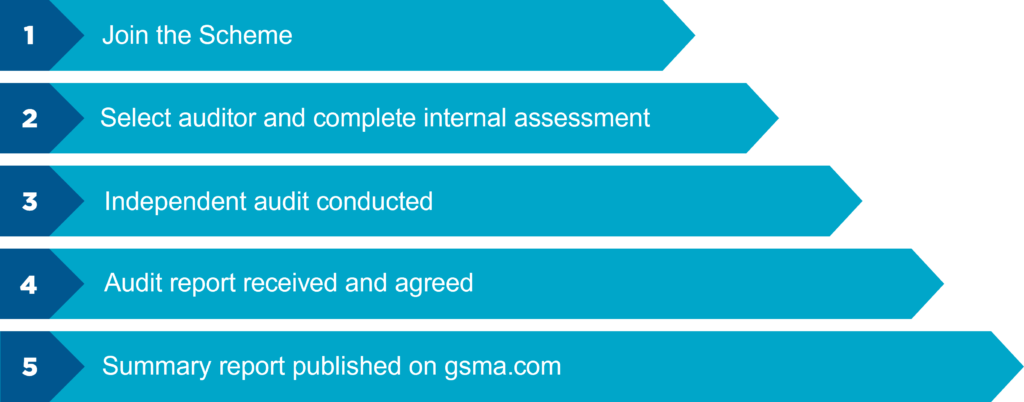
NESAS defines how the assessment is performed and it consists of two steps. The first is where the vendor carries out a self-assessment. If they believe their processes meet the requirements, they can claim conformance. The second step involves an independent auditing company. They assess if the processes satisfy the security requirements and verify if the vendor is applying their processes.
The GSMA appoint the auditing companies and equipment vendors can choose theirs from the shortlist. The GSMA appoints competent auditors based on eligibility criteria, following a competitive proposal process.
If you would like to know more or speak to someone about the scheme, please get in touch.